Are you fascinated by the world of cybersecurity? Do you dream of using your tech skills for good and making a difference in the digital realm? If so, then embarking on the path of an ethical hacker could be your calling!
Ethical hackers, also known as white-hat hackers, play a crucial role in ensuring the security of computer systems and networks. They use their expertise to identify vulnerabilities, test security measures, and protect against cyber threats. It's a rewarding and dynamic field that offers endless opportunities for growth and impact.
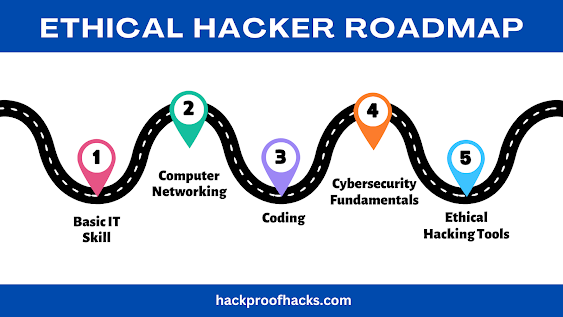
But how do you get started on this exciting journey? Here's a roadmap to guide you:
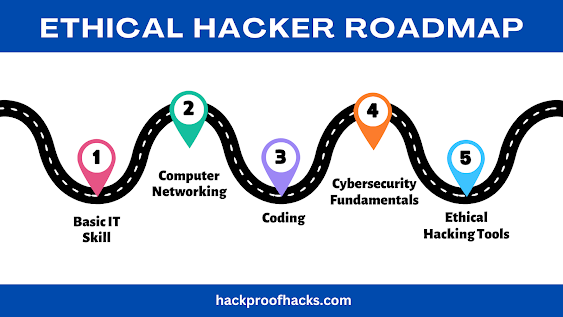
- Build Your Knowledge: Start by learning the fundamentals of computer science, cybersecurity, and networking. Take online courses, read books, and immerse yourself in hands-on projects to develop a strong foundation.
- Hands-On Practice: Dive into cybersecurity labs, challenges, and simulations to apply your knowledge in real-world scenarios. Practice using ethical hacking tools and techniques to sharpen your skills.
- Get Certified: Consider earning certifications like Certified Ethical Hacker (CEH), CompTIA Security+, or Offensive Security Certified Professional (OSCP) to validate your expertise and enhance your credibility.
- Specialize: Explore different areas within ethical hacking, such as penetration testing, digital forensics, or security analysis. Find your passion and focus on mastering that niche.
- Network: Connect with fellow hackers, cybersecurity professionals, and industry experts through online forums, social media, and networking events. Building a strong network can open doors to opportunities and collaborations.
- Stay Updated: Stay abreast of the latest cybersecurity trends, threats, and technologies. Attend conferences, webinars, and training programs to keep your skills sharp and relevant.
- Ethical Conduct: Always adhere to ethical standards and legal boundaries in your hacking activities. Obtain proper authorization before testing systems and respect privacy and data protection laws.
Want free resources or want to dive deep into every step of this roadmap? Click here to read our comprehensive guide on how to become an ethical hacker.
.jpg)
Comments
Post a Comment